May 29, 2026
Your operations deserve protection that never stops
Prevention-first OT security across 3,600+ deployments, engineered for zero operational disruption.

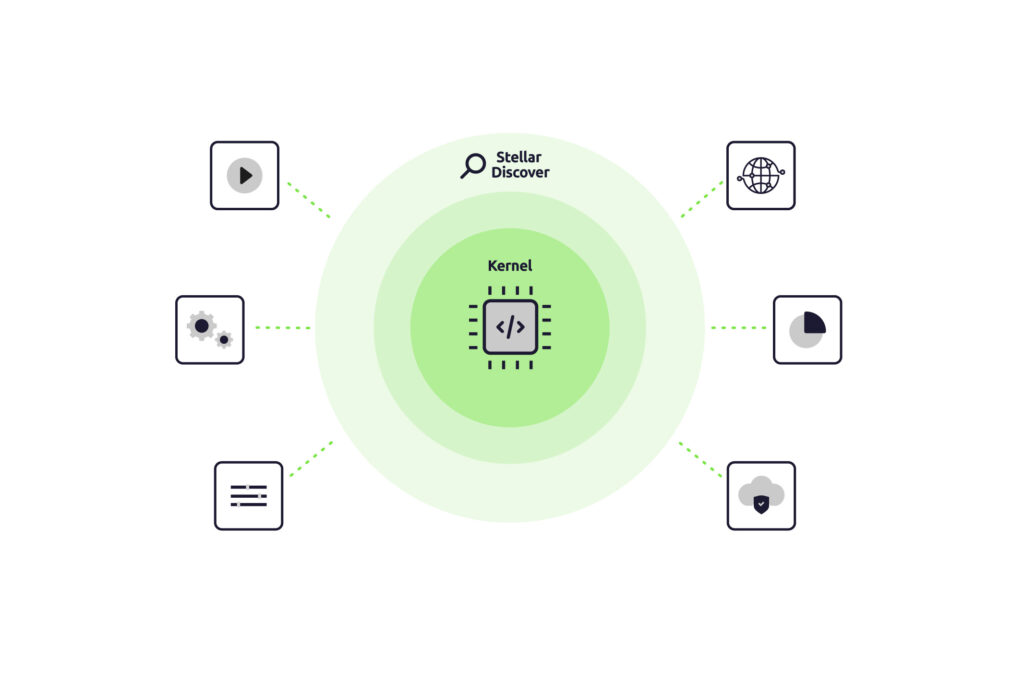
Safe OT endpoint visibility, without disrupting operations. Stellar Discover is a detection-only sensor that runs entirely in user space, with no kernel access, and no system interference. It deploys in about a minute, requires no reboot, and co-exists with the IT EPP/EDR you may already run. A complete picture of every OT endpoint that even the most cautious operator will say yes to.
Operates at guest privilege level, as safe as Windows Notepad.
No reboot, no driver, no configuration.
No conflict with CrowdStrike, Defender, SentinelOne, or any other endpoint stack you already run.
No system interference at runtime.

Hardware, OS, network flow records, and full software inventory across every managed asset.
Identify how many devices are infected with malware and continue monitoring to see if the infection worsens.
Data feeds directly into SenninOne, where it is prioritized using VSAR (Vulnerability Situational Awareness Rating) for production-aware decisions.
Tracks USB insertion records and login failures, two of the most telling early indicators of compromise on the plant floor.

Illuminates the OT endpoint blind spots alongside IT EPP/EDR.
Discover is a sensor, by design.
Telemetry feeds StellarOne for VSAR-prioritized vulnerability management at enterprise scale.
Centrally managed through the StellarOne console.


Licensing:
Stellar Discover is licensed at a fixed price for unlimited seats per six-month term. Contact your TXOne representative or partner for current pricing and trial details.
Platform support:
Connectivity:
Connected, intermittent, and air-gapped environments are fully supported. Consult TXOne or a certified implementation partner for deployment guidance.
Deploy Stellar Discover across your OT endpoints in a single maintenance window. No drivers. No kernel access. No reboot. See what is running on systems that previously rejected agents.
Prevention-first OT security across 3,600+ deployments, engineered for zero operational disruption.