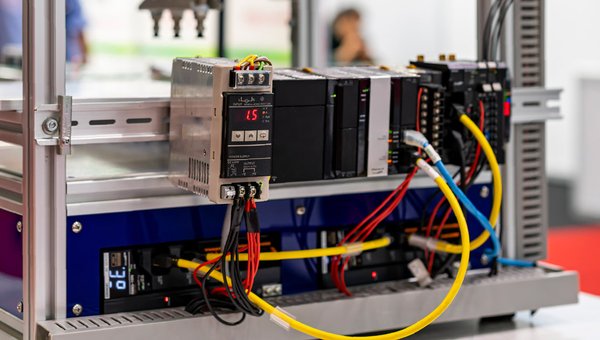
Internet-Exposed PLCs: Addressing the Risks Behind the Headlines
The Exposure That Predates the Headlines Recent advisories and reporting have highlighted cyber activity targeting internet-facing Operational Technology devices, particularly Rockwell Automation and Allen-Bradley PLCs such as CompatLogix and Micro850 models. While media coverage tends to focus on who may be behind these campaigns, the more important question for industrial organizations is: why are these… Read more