Discover: You Can't Secure What You Can't See
Part 1 of the Discover. Assess. Protect. series
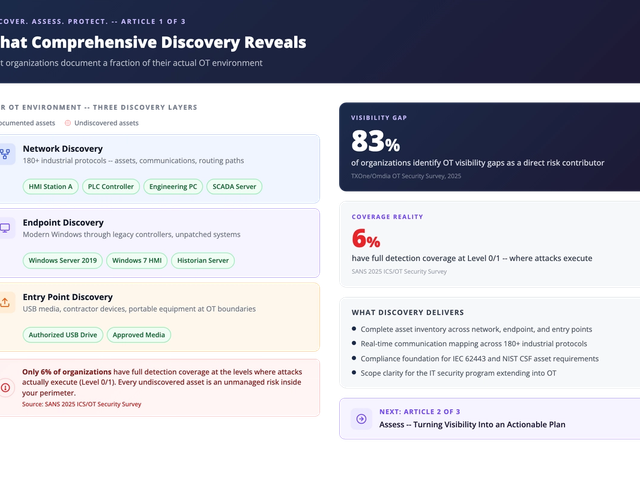
Most security programs start with a confident assumption: we know what's in our environment. The data tells a different story. 83% of organizations identify OT visibility gaps as a direct risk contributor (TXOne/Omdia OT Security Survey, 2025). Only 6% have full detection coverage at the levels where attacks actually execute (SANS 2025 ICS/OT Security Survey).
You cannot protect what you cannot see. And in most OT environments, there is far more hidden than visible.
What "Discover" actually means
Discovery is not a one-time inventory exercise. It is the continuous process of identifying assets, mapping communication patterns, and understanding the dependencies that keep operations running.
Effective OT discovery works across every layer of the environment:
- Network discovery identifies assets and protocol usage across 180+ industrial protocols, revealing what is communicating, with what, and how often.
- Endpoint discovery catalogs every system in the environment, from modern Windows servers to legacy controllers running decades-old operating systems.
- Entry point discovery tracks devices and media arriving at OT boundaries, including USB drives, contractor laptops, and portable equipment.
- Unified visibility brings network, endpoint, and entry point findings together into a single operational view.
The result is not just an asset list. It is a real-time understanding of your operational environment and the risks within it.
Why discovery changes your security posture
Consider this: a manufacturing facility documents 80 OT endpoints in its asset management system. After comprehensive discovery, it finds 100. Those 20 additional systems had never been patched, never been monitored, and were communicating across network segments nobody authorized. This is typical. Organizations routinely discover significantly more connected devices than their asset registers account for (Omdia 2025 OT Cybersecurity Platforms Research). Every undiscovered asset is an unmanaged risk sitting inside your perimeter.
For IT security leaders extending their program into OT, discovery answers the foundational question: What is the actual scope of the environment I am responsible for?
Discovery also builds the foundation for compliance. Frameworks like IEC 62443 and NIST CSF require a complete asset inventory as their starting point. Without discovery, compliance is based on assumptions rather than evidence.
Seeing is necessary, but not sufficient
A comprehensive asset inventory is a critical first step. But visibility alone does not reduce risk. When discovery reveals 200 vulnerabilities across your OT environment, the next question is not "how do we fix all of them?" It is "which ones matter most, given our operational constraints?"
That question is the domain of assessment, where discovery findings become a prioritized, operational-context plan your teams can act on.
Next in the series: Assess: Turning Visibility Into an Actionable Plan
Ready to start? A SenninRecon assessment maps your OT environment passively, with no agents and no inline deployment, giving you results in days rather than months.
Tags
About the Author

At the heart of Dan’s mission is the belief that OT security should empower businesses to operate without compromise, balancing risk management with operational integrity. His insights have helped organizations reframe security challenges, ensuring their solutions are as practical as they are innovative.