See Every OT Asset. Score Every Risk in Operational Context.
Turn OT unknowns into a prioritized action plan.
TXOne SenninRecon discovers OT assets through passive network listening and scores vulnerabilities in operational context with VSAR. No active scans that crash PLCs. No agents. Evidence-based remediation tickets with one-day response.
Most OT security programs begin with an honest admission: we do not know what we have, and we do not know what is at risk. SenninRecon answers both questions without touching production systems.
Traditional vulnerability scanners are dangerous in OT. Active IT scanners crash PLCs, saturate fieldbus networks, and trigger safety systems. Your operations team refuses them, correctly. SenninRecon discovers assets through passive network listening combined with optional safe queries only where explicitly approved. VSAR scores vulnerability severity using CVSS, EPSS, real-world attack telemetry, and TXOne threat intelligence. SenninRecon then layers operational context so a critical CVE on an air-gapped system with virtual patch coverage ranks lower than a moderate CVE on a network-facing asset. If you have already invested in a network visibility platform, SenninRecon adds the asset-level assessment and operational-context prioritization it cannot provide. Findings include IEC 62443-3-3 gap analysis and align with the NIST CSF Identify function so your next security review starts with evidence.
PRODUCT STORY
Assessment That Does Not Become the Incident
Your operations team has watched active scanners crash production before. That memory is why IT vulnerability scanners are rejected at the OT boundary. SenninRecon was built around the opposite assumption: the appliance should never become the event. Passive discovery by default. Safe queries only where operations explicitly approves them. VSAR scoring that reflects the reality of air-gapped systems, virtual patch coverage, and compensating controls. Asset-linked tickets your engineers can actually act on. An assessment report your CFO will actually read, and that funds the next security investment on the basis of what your program actually needs.
Passive-By-Default
Architecturally safe for PLCs, SCADA workstations, and safety systems.
VSAR Operational Context
VSAR severity scoring paired with prioritization that reflects air-gap, exposure, patch coverage, and asset criticality.
Land and Expand
The entry point that funds Edge, Stellar, or Element investments on evidence.
Continuous Posture
Reassessment as assets and firmware change, not a point-in-time binder.
BY THE NUMBERS
THE CHALLENGE
OT Security Challenges
Critical challenges that SenninRecon is purpose-built to solve
01 / 04
Your Asset Inventory Is Out of Date Before the Next Audit
Manual spreadsheets and periodic walk-downs cannot keep pace with equipment changes, vendor swaps, and contractor work. Your compliance auditor arrives and the inventory you are required to maintain is already incorrect.
Your Asset Inventory Is Out of Date Before the Next Audit
Manual spreadsheets and periodic walk-downs cannot keep pace with equipment changes, vendor swaps, and contractor work. Your compliance auditor arrives and the inventory you are required to maintain is already incorrect.
Key Features
Discover how SenninRecon protects your OT environment
01 / 06
Passive Discovery That OT Teams Accept
Your operations team has seen active scanners crash production before. SenninRecon discovers assets through passive network listening, with optional safe queries only where explicitly approved. No traffic storms. No controller lockups. No production risk. The appliance deploys in hours and begins building your asset picture inside your next maintenance window.
Key Capabilities
Passive Discovery That OT Teams Accept
Your operations team has seen active scanners crash production before. SenninRecon discovers assets through passive network listening, with optional safe queries only where explicitly approved. No traffic storms. No controller lockups. No production risk. The appliance deploys in hours and begins building your asset picture inside your next maintenance window.
Key Capabilities
Real-World Applications
See how organizations deploy SenninRecon in production environments
01 / 04
Start an OT Security Program From Evidence
Organizations beginning their OT security journey deploy SenninRecon first. The assessment answers the two questions every program starts with: what do we have, and what is at risk? Findings scope the next investment honestly, on the basis of documented reality.
Start an OT Security Program From Evidence
Organizations beginning their OT security journey deploy SenninRecon first. The assessment answers the two questions every program starts with: what do we have, and what is at risk? Findings scope the next investment honestly, on the basis of documented reality.
TECHNOLOGY
Technology
Technologies powering SenninRecon
Passive Discovery Architecture
Zero-Disruption Asset Discovery for OT
SenninRecon discovers OT assets through passive traffic analysis and optional safe active queries. No kernel drivers, no intrusive scanning, no risk to production. Active IT scanners flood OT networks with probes that crash PLCs and HMIs. SenninRecon is designed to respect the operational reality of industrial networks.
- Passive traffic analysis for zero-disruption discovery
- Safe active queries with OT-aware throttling
- No risk of crashing PLCs or HMIs during scan
- Designed for production networks, not IT subnets
Passive-first discovery architecture purpose-built for OT, not an active IT scanner repackaged.
OT VS IT
Active IT Scanners vs. SenninRecon Passive OT Assessment
IT vulnerability scanners were never designed for industrial networks. SenninRecon is purpose-built to discover OT safely.
Discover OT assets without crashing PLCs or HMIs
Active IT scanners flood networks with probes; known to crash industrial devices
Passive-first discovery with optional OT-aware safe active queries
Recognize industrial protocols at command level
Port-only filtering; Modbus or DNP3 treated as generic TCP traffic
180+ industrial protocols with command-level deep packet inspection
Prioritize findings by operational context
CVSS-only ranking with no awareness of exposure path or compensating controls
VSAR scores severity from real attack data; SenninRecon prioritizes by asset criticality, exposure path, and virtual patch coverage
Operate without endpoint agents
Authenticated scans require credentials and sometimes agents, often unacceptable in OT
No agents, no credentials required; SPAN/mirror port only
Deliver actionable remediation, not raw CVE lists
CVE dumps create analysis paralysis; no operational prioritization
Prioritized remediation with clear next actions and ownership
Path from assessment to continuous governance
Point-in-time audit; no integration with enterprise OT security program
Natural expansion path into SenninOne for continuous governance
Discover OT assets without crashing PLCs or HMIs
Active IT scanners flood networks with probes; known to crash industrial devices
Passive-first discovery with optional OT-aware safe active queries
Recognize industrial protocols at command level
Port-only filtering; Modbus or DNP3 treated as generic TCP traffic
180+ industrial protocols with command-level deep packet inspection
Prioritize findings by operational context
CVSS-only ranking with no awareness of exposure path or compensating controls
VSAR scores severity from real attack data; SenninRecon prioritizes by asset criticality, exposure path, and virtual patch coverage
Operate without endpoint agents
Authenticated scans require credentials and sometimes agents, often unacceptable in OT
No agents, no credentials required; SPAN/mirror port only
Deliver actionable remediation, not raw CVE lists
CVE dumps create analysis paralysis; no operational prioritization
Prioritized remediation with clear next actions and ownership
Path from assessment to continuous governance
Point-in-time audit; no integration with enterprise OT security program
Natural expansion path into SenninOne for continuous governance
SenninRecon brings Security Improvement That Can Actually Be Done: safe OT discovery, operational risk prioritization, and a direct path from assessment to enterprise governance.
HOW IT WORKS
Deploy SenninRecon in 5 Steps
A streamlined implementation process designed for OT environments with zero disruption to operations.
Week 1: Install SenninRecon appliance and connect to SPAN or mirror ports on the OT network segment
Week 2: Complete initial passive discovery; review first asset inventory and VSAR risk scores
Week 3-4: Configure optional safe active queries and prioritize remediation actions by operational context
Month 2: Deliver assessment report with prioritized remediation roadmap and compliance gap analysis
Ongoing: Continuous posture monitoring; expansion path to SenninOne for enterprise governance
Operational & Protected
TECHNICAL SPECS
Technical Specifications
INTEGRATIONS
Seamless Integration with SenninRecon
Designed to integrate into existing OT infrastructure without disrupting operations.
CUSTOMER OUTCOMES
Customer Success

“Thanks to OT security solution Stellar, TXOne Networks helps us mitigate risks that we couldn't address yesterday without making significant financial investments.”

“Today, every change to assets is optimally managed. Machines are eff ectively “locked down,” and no update is applied without prior checks.””
LEARN MORE
Related Resources
Explore resources related to SenninRecon
TXOne SageOne datasheet
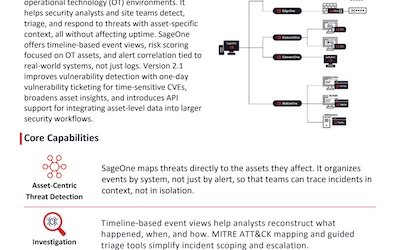
Security Operations for OT Environments SageOne is TXOne Networks’ centralized investigation and visibility platform for operational technology (OT) environments. It helps security analysts and site teams detect, triage, and respond to threats with asset-specific context, all without affecting uptime. SageOne offers timelineㄦbased event views, risk scoring focused on OT assets, and alert correlation tied to… Read more

Annual OT/ICS Cybersecurity Report 2024
As the line between IT and OT continues to blur, new efficiencies are unlocked in tandem with new risks—namely, supply chain vulnerabilities, aging infrastructure, patching difficulties, and gaps in incident response. These challenges are the main focus of our Annual OT/ICS Cybersecurity Report, which is grounded in a large-scale survey conducted jointly by TXOne Networks… Read more

OT Patch Management Playbook: Defend Without Disruption
Operational Technology (OT) environments are the backbone of critical infrastructure, encompassing industries such as manufacturing, utilities, energy, as well as food and beverage. OT encompasses hardware and software designed to monitor and control physical equipment, processes, and events within organizations. These systems are typically built for longevity, often operating for over a decade. However, these… Read more
See All Resources
Browse all resources related to senninrecon
RELATED PRODUCTS
NEXT STEP
Start With What You Have. Score What You Need to Fix.
Request a SenninRecon assessment to see every asset, score every risk in operational context, and receive a prioritized remediation plan your team can actually execute.

