Enterprise OT Governance From a Single Console
Unified orchestration across Edge, Stellar, and Element from a single console.
Enterprise orchestration platform built for 500 to 100,000+ OT asset environments. VSAR risk scoring, MITRE ATT&CK for ICS mapping, and approval workflows that bridge IT security and OT operations.
67% of organizations struggle with unified IT/OT visibility. Sennin closes that gap.
Managing OT security across distributed sites means coordinating Edge network appliances, Stellar endpoint agents, and Element inspection devices, often with separate consoles and fragmented visibility. Sennin unifies all TXOne deployments into a single orchestration platform with VSAR vulnerability scoring that prioritizes remediation by operational context, approval workflows that ensure no policy deploys without operational sign-off, and MITRE ATT&CK for ICS mapping that correlates events across every security layer. Built for 500 to 100,000+ asset environments.
PRODUCT STORY
Centralized OT Security Governance
Sennin delivers enterprise-wide visibility and governance across the TXOne solution portfolio — Edge network security, Stellar endpoint protection, Element security inspection, and SenninRecon discovery and assessment. For organizations managing OT security across multiple sites and product families, Sennin provides the single source of truth for security posture, compliance status, and operational metrics.
Cross-Product Visibility
Unified dashboard across network, endpoint, and inspection security — not just one product family.
Multi-Site Governance
Enterprise-scale management across global manufacturing and critical infrastructure operations.
Compliance Reporting
IEC 62443-3-3 gap analysis when SenninRecon is deployed, plus NIST CSF alignment for your security program.
BY THE NUMBERS
THE CHALLENGE
OT Security Challenges
Critical challenges that Sennin is purpose-built to solve
01 / 04
Fragmented Security Visibility
Your network security generates alerts in one console. Endpoint protection reports to another. Inspection data lives in a third. Critical threats hide in the visibility gaps while your team switches between dashboards.
Fragmented Security Visibility
Your network security generates alerts in one console. Endpoint protection reports to another. Inspection data lives in a third. Critical threats hide in the visibility gaps while your team switches between dashboards.
Key Features
Discover how Sennin protects your OT environment
01 / 06
Asset-Centric Threat Detection
Sennin maps threats directly to the assets they affect, organizing security events by production system rather than alert severity. Your team traces incidents in operational context, understanding which systems are impacted and why they matter to business continuity before making response decisions.
Key Capabilities
Asset-Centric Threat Detection
Sennin maps threats directly to the assets they affect, organizing security events by production system rather than alert severity. Your team traces incidents in operational context, understanding which systems are impacted and why they matter to business continuity before making response decisions.
Key Capabilities
Real-World Applications
See how organizations deploy Sennin in production environments
01 / 06
Semiconductor Manufacturing
Zero-disruption monitoring of sensitive fab equipment. Protect cleanroom systems that cannot tolerate disruptions while achieving complete security visibility without operational impact.
Semiconductor Manufacturing
Zero-disruption monitoring of sensitive fab equipment. Protect cleanroom systems that cannot tolerate disruptions while achieving complete security visibility without operational impact.
DEPLOYMENT OPTIONS
Deployment Options
Choose the right deployment model for Sennin
On-Premises Virtual Appliance
Deploy Sennin in your data center for complete control over enterprise security governance data and compliance reporting.
TECHNOLOGY
Technology
Technologies powering Sennin
Enterprise Dashboard
Cross-Product Security Posture
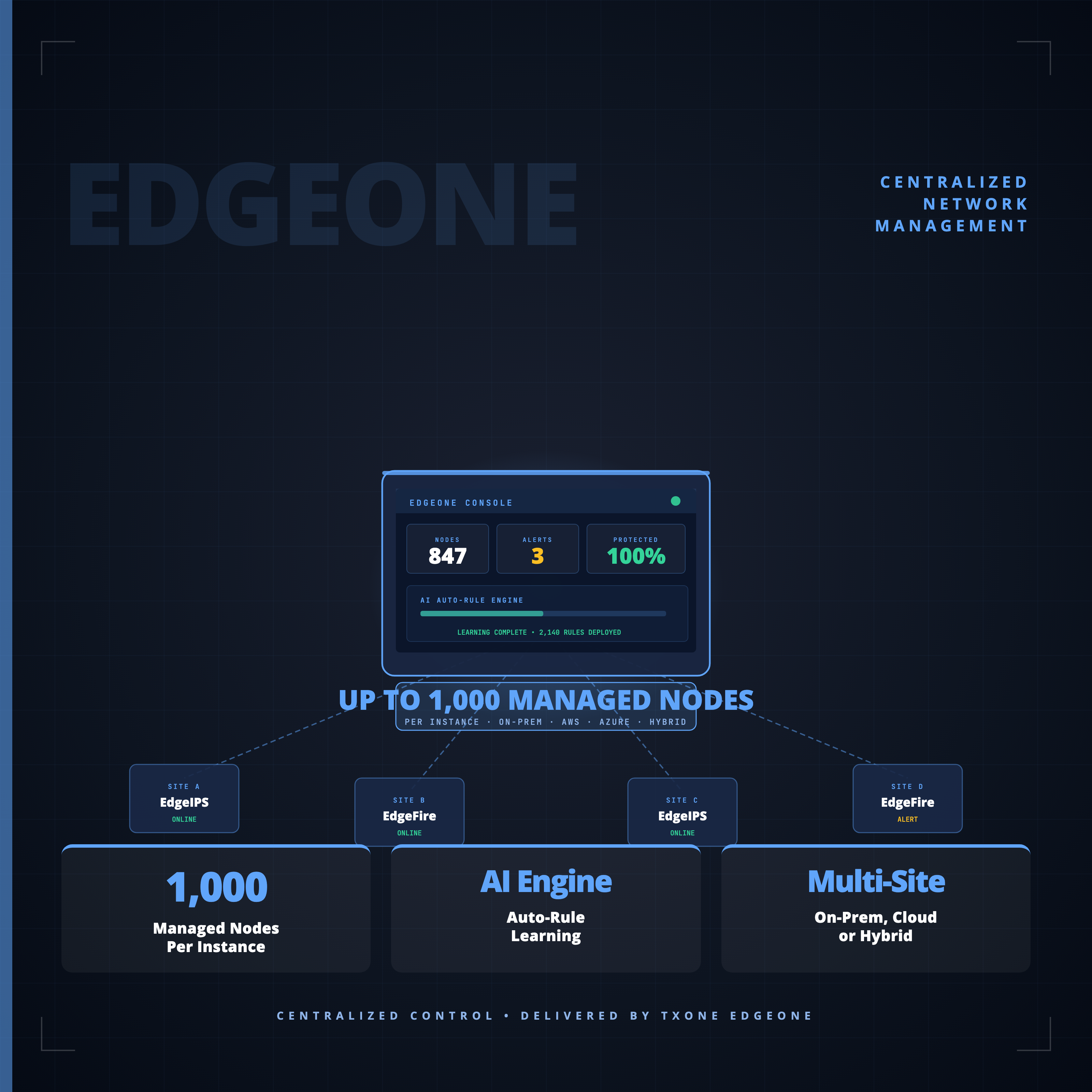
Sennin aggregates data from EdgeOne, StellarOne, and ElementOne consoles to provide a unified view of OT security posture across all product families and deployment sites.
- Real-time security posture scoring
- Cross-product threat correlation
- Site-by-site comparison
- Executive reporting
The only OT security platform providing unified visibility across network, endpoint, and inspection.
HOW IT WORKS
Deploy Sennin in 4 Steps
A streamlined implementation process designed for OT environments with zero disruption to operations.
Week 1: Deploy Sennin virtual appliance without network changes
Week 2-3: Connect existing TXOne products for unified telemetry
Month 1: Configure asset-centric views and vulnerability workflows
Ongoing: Expand coverage as TXOne deployment grows
Operational & Protected
TECHNICAL SPECS
Technical Specifications
INTEGRATIONS
Seamless Integration with Sennin
Designed to integrate into existing OT infrastructure without disrupting operations.
CUSTOMER OUTCOMES
Customer Success

“Thanks to OT security solution Stellar, TXOne Networks helps us mitigate risks that we couldn't address yesterday without making significant financial investments.”

“Today, every change to assets is optimally managed. Machines are eff ectively “locked down,” and no update is applied without prior checks.””
LEARN MORE
Related Resources
Explore resources related to Sennin
TXOne SageOne datasheet
Security Operations for OT Environments SageOne is TXOne Networks’ centralized investigation and visibility platform for operational technology (OT) environments. It helps security analysts and site teams detect, triage, and respond to threats with asset-specific context, all without affecting uptime. SageOne offers timelineㄦbased event views, risk scoring focused on OT assets, and alert correlation tied to… Read more

Annual OT/ICS Cybersecurity Report 2024
As the line between IT and OT continues to blur, new efficiencies are unlocked in tandem with new risks—namely, supply chain vulnerabilities, aging infrastructure, patching difficulties, and gaps in incident response. These challenges are the main focus of our Annual OT/ICS Cybersecurity Report, which is grounded in a large-scale survey conducted jointly by TXOne Networks… Read more

OT Patch Management Playbook: Defend Without Disruption
Operational Technology (OT) environments are the backbone of critical infrastructure, encompassing industries such as manufacturing, utilities, energy, as well as food and beverage. OT encompasses hardware and software designed to monitor and control physical equipment, processes, and events within organizations. These systems are typically built for longevity, often operating for over a decade. However, these… Read more
See All Resources
Browse all resources related to sennin
RELATED PRODUCTS
NEXT STEP
Ready for Unified OT Security Management?
See how Sennin orchestrates security across Edge, Stellar, and Element deployments at enterprise scale. Request a platform demonstration.