Get a personalized deployment recommendation based on your specific industrial environment and security requirements.

Your Operations Deserve Protection That Never Stops
Prevention-first OT security across 3,600+ deployments, engineered for zero operational disruption.
One Architecture. Complete Protection.
TXOne Complete unifies TXOne Edge network security, TXOne Stellar endpoint protection, TXOne Element inspection, and TXOne Sennin orchestration into a single architecture designed for industrial environments. Discover builds the inventory. Assess builds the enforcement sequence. Protect applies inline prevention that blocks threats in sub-seconds across every asset in your environment. Shared threat intelligence. Coordinated response. Single accountability.
Network Defense
TXOne Edge
Discover
Map your network topology and identify every connected asset across 180+ industrial protocols spanning IT and OT networks. Agentless discovery gives you complete network visibility without impacting production traffic.
Assess
Identify network vulnerabilities and coverage gaps across industrial control system communication paths, including legacy protocols and IT/OT convergence zones that IT-native tools cannot see. Protocol-level analysis surfaces exposures that port-and-protocol filtering misses and feeds them directly into Edge enforcement policies.
Protect
Deploy IPS with 1,500+ OT-native threat signatures, virtual patching for systems that cannot receive vendor updates, and micro-segmentation at the protocol level. TXOne Edge blocks threats in sub-seconds, eliminating the detection-to-enforcement gap that attackers rely on during manual response workflows. Fail-safe hardware bypass guarantees continuous operation even if the security device itself fails.

Endpoint Protection
TXOne Stellar
Discover
Inventory every endpoint from Windows XP through Windows 11 and common Linux distributions, then establish automated behavioral baselines unique to each device. TXOne Stellar deploys without a reboot, without agent conflicts, and without touching your production schedule.
Assess
Evaluate endpoint coverage and surface your highest-risk legacy assets, ranked by operational criticality rather than patch status alone. With 44.6% of OT organizations running environments where more than half of all endpoints are legacy Windows,2 and 78.2% of those systems classified as critical or high-value assets,3 unprotected legacy endpoints are not an edge case. They are your most targeted attack surface.
Protect
Enforce application control and OT-native behavioral anomaly detection (CPSDR) to prevent unauthorized changes from reaching production. Production-aware policy enforcement operates within the resource constraints of legacy Windows and Linux endpoints, delivering active protection without the resource consumption that causes IT endpoint tools to crash legacy production systems.

Security Inspection
TXOne Element
Discover
Inspect every device and removable media before they enter your environment. No software to install. No system to modify. No network connection required. Every scanned device is automatically added to your asset inventory, creating an auditable record of what entered your facility and when.
Assess
Validate the security posture of portable media and transient devices with deep scanning at 7,200 files per minute. TXOne Element automatically flags changes in device configuration or content detected since the last scan, surfacing unplanned modifications before they reach your production network.
Protect
Block supply chain threats and contaminated media from reaching production with air-gap-compatible, zero-footprint inspection. No agent installation. No system modification. No network connectivity required. Protection that works within your operational constraints, not despite them.

Enterprise Orchestration
TXOne Sennin
Discover
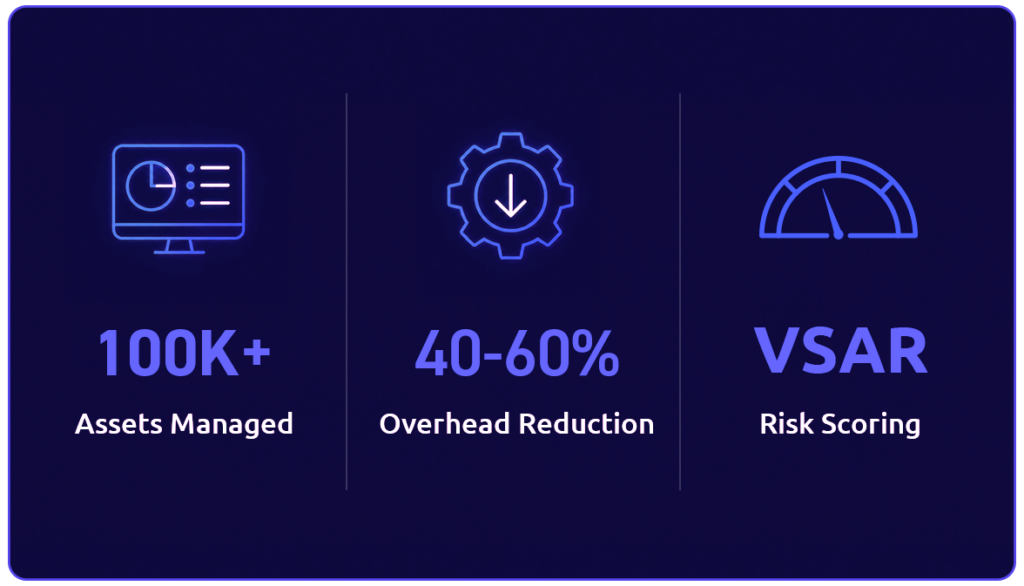
Centralized asset visibility across every site and zone. TXOne Sennin, extended with SenninRecon, automates asset discovery across your full environment, surfaces vulnerabilities with operational context, and generates risk scores that reflect real exposure rather than raw CVE severity, all from a single console.
Assess
SenninRecon continuously discovers assets and feeds vulnerability data into VSAR risk scoring, which prioritizes exposures based on operational context rather than raw CVSS severity. A critical CVE on an air-gapped system with active virtual patch coverage ranks lower than a moderate CVE on a network-facing asset with no compensating controls in place.
Protect
Coordinated policy governance across TXOne Edge, TXOne Stellar, and TXOne Element with workflows that ensure policy deploys with the correct operational sign-off. As protections activate, VSAR risk scores update continuously, giving security and operations teams measurable, ongoing proof that posture is improving across every site.

“Thanks to OT security solution Stellar, TXOne Networks helps us mitigate risks that we couldn’t address yesterday without making significant financial investments.” Read the story
Chris Thompson
Director of Brewery OT Security at Carlsberg Group
Awards & Recognition
Industry analysts and award bodies recognize TXOne Networks for OT security leadership.

Your Path to Unified Protection
Whether you need the strategic picture, technical validation, or business case, every conversation shows what unified OT security delivers for your environment
Strategic Assessment
We map your current security architecture, identify vendor fragmentation gaps, and demonstrate what unified protection delivers for your specific environment. Clear recommendations with measurable outcomes.
Technical Proof of Value
Deploy TXOne in your environment and see visibility results in 60 minutes. Identify your highest-risk assets with operational context. Activate prevention with hardware bypass guaranteeing zero disruption.
Business Case Development
Quantify your vendor coordination costs, fragmentation risks, and legacy system exposure. Get the ROI analysis and cost avoidance calculations you need to justify unified protection investment.
See What Unified OT Security Delivers
Your current security stack has gaps that fall between vendors. Our team maps your environment, shows you where coverage breaks down, and walks you through how unified protection closes those gaps without disrupting production.