Comprehensive Analysis of New Attack Vectors for Modern ICS Environments
Background
Reflecting on the characteristics and trends of automated factories, here are the technologies that often require programming: Controller, Industrial Robot, Computer Numerical Control, Additive Manufacturing, Augmented Reality, and more (for related introductions and use cases, please refer to [1]). These features can be installed in a development environment on a computer by programmers or system integrators, who can then adjust asset behavior according to the factory’s production needs. For example, in Computer Numerical Control (CNC), engineers can first design the physical object of the desired product component using Computer-Aided Design (CAD), then generate G-code (NC-code, used to command machine actions) with Computer-Aided Manufacturing (CAM), and finally download the code to the CNC machine to complete the manufacturing process of raw materials (such as metal, wood, plastic, ceramics, or composite materials) without human intervention. Similarly, in the case of Industrial Robots, engineers can not only program directly next to the robot using a pendant (refer to [2] for detailed robot structure), but engineers can also install a development environment in a computer (commonly called Off-Line programming, OLP), enabling them to set the desired robot behaviors in an offline state. After testing and confirming that there are no issues, the program can then be uploaded to the actual robot for execution.
 Figure 1. Schematic of Technologies Used in Automated Factories
Figure 1. Schematic of Technologies Used in Automated Factories
To facilitate explanation, we will first divide the operation process of each technology into three parts: Part 1 is the development environment installed on the computer by engineers; Part 2 is the code written (or compiled) through this environment; and Part 3 is the asset that actually executes the program code. As all three parts play a core role in their respective technologies, many researchers have devoted extensive research to them in the past [3] to [12].
For example, in most ICS/OT environments, many assets often enable insecure or unauthenticated services due to specific considerations. These services have the ability to directly control the operation of physical assets. In the case of Additive Manufacturing, if an attacker controls an asset to overheat a certain material, it could potentially lead to a fire in the factory. Similarly, in the case of Industrial Robots, if an attacker controls the robotic arm to perform unexpected actions, it could potentially injure nearby operators.
Furthermore, concerning the code aspect, Trend Micro researchers found that proprietary programming languages provided by industrial robot manufacturers, in addition to basic movement instructions, sometimes allow for dynamic code loading functionality (e.g., ABB, Comau, Denso, and Fanuc, etc.). This enables attackers to download malicious code to the robot’s controller and laterally move it to other robots under difficult-to-detect circumstances, taking over the entire factory [11].
Regarding the development environment, cybersecurity researchers have found that some vendors (such as Rockwell Automation, Schneider Electric, and GE) do not perform integrity checks on project files transmitted from the PLC to the computer. This makes it possible for engineers to load code that is controlled by an attacker onto the PLC, causing the computer to be attacked by ransomware [8]. However, from past research, we find that discussions on robot OLP-related issues are relatively scarce. Therefore, we will discuss its relevant threats and the latest submission (as of April 2023) of TXOne Networks by FANUC ROBOGUIDE-HandlingPRO Path Traversal Vulnerability (CVE-2023-1864) [13].
Robot OLP Vulnerability Analysis
Compared to the development environment of other technologies, robot OLP (Offline Programming) usually comes equipped with a 3D simulator to allow for precise testing before uploading programs to an actual industrial robot. In addition to displaying the robot’s motion, analyzing accessibility, and testing for collision issues, the OLP can also assist engineers in creating optimal robot execution paths. This achieves benefits of small-batch automation production that were previously unattainable with industrial robots that required manual programming using a pendant while online.
Given this, most modern industrial robot manufacturers have their own OLP platform that allows engineers to directly write code in the brand’s proprietary programming language or use a graphical drag-and-drop approach to automatically generate the programming language. Figure 2 shows an example of HWIN robot manufacturer’s self-developed OLP.
 Figure 2. OLP of HWIN Robot Manufacturer
Figure 2. OLP of HWIN Robot Manufacturer
Source: HWIN Official User Manual
 Figure 3. Tesla Factories Use Robots from Different Manufacturers for Their Manufacturing Processes (KUKA And FANUC)
Figure 3. Tesla Factories Use Robots from Different Manufacturers for Their Manufacturing Processes (KUKA And FANUC)
Source: Tesla Official Twitter
However, modern factories do not rely solely on robots from a single manufacturer for their manufacturing processes. For example, in advanced Tesla factories, they use multiple KUKA robots to perform stamped parts & chassis castings tasks, while also employing FANUC robots to transfer vehicle bodies to the paint shop [14]. Since different manufacturers have proprietary programming languages, to avoid engineers having to learn multiple types of programming languages simultaneously, many manufacturer-independent robot OLP platforms have been developed. These platforms provide a realistic simulator, considered one of the most important developments in OLP. RoboDK is an example of such a platform.
RoboDK has a library of over 500 robots from more than 50 different manufacturers, including ABB, FANUC, KUKA, Motoman, Hwashi Robots, and Universal Robots, among others. It allows engineers to first design the robot’s behavior using a simulator, and then generate corresponding language formats for different brands. Figure 4 shows an example of using RoboDK to generate the language format for a KUKA robot.
 Figure 4. Generating KUKA Robot Language Format Using RoboDK
Figure 4. Generating KUKA Robot Language Format Using RoboDK
Source: RoboDK Official Website
Taking FANUC’s ROBOGUIDE – HandlingPRO as an example, not only can it compile programs and simulate robot movements for the robots, but it also provides further services that allow engineers to simulate the use of a pendant to operate the robot, either locally or remotely. This enables engineers to clearly predict the scenarios that factory operators will face once the program is deployed on a real robot, as shown in Figures 5 and 6.
 Figure 5. ROBOGUIDE – HandlingPRO Local Simulation of Using a Pendant to Operate the Robot
Figure 5. ROBOGUIDE – HandlingPRO Local Simulation of Using a Pendant to Operate the Robot
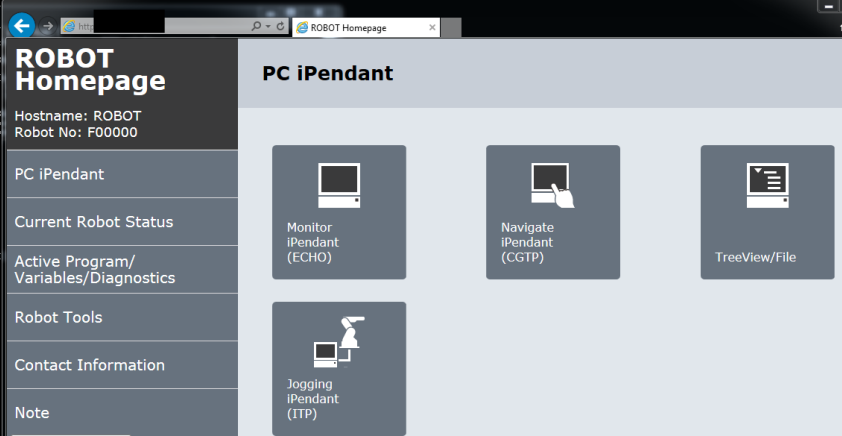 Figure 6. ROBOGUIDE – HandlingPRO Remote Simulation Uses Pendant to Operate the Robot
Figure 6. ROBOGUIDE – HandlingPRO Remote Simulation Uses Pendant to Operate the Robot
As mentioned earlier, advanced robot OLPs also serve as a breeding ground for new types of cyber threats. As shown in the right half of Figure 7, in the past, attackers mostly needed access to the internal factory network to launch attacks through robots. However, as shown in the left half of Figure 7, when a programmer or integrator uses an OLP with remote services enabled, their computers are exposed to remote attack threats. At the same time, the computers of programmers or integrators are not permanently isolated within the factory’s internal network, providing attackers with the opportunity to attack their computer equipment without having to access the internal factory network. Furthermore, as integrators need to maintain robot assets in multiple factories simultaneously, they inevitably carry potentially compromised computers in and out of other factories, which could significantly expand the negative impact that attackers can have.
 Figure 7. New Type of Cyberattack Vectors
Figure 7. New Type of Cyberattack Vectors
While studying the advanced features provided by ROBOGUIDE – HandlingPRO, we found that, like most robots without authentication mechanisms, its simulator also inherits such threats. Attackers can easily connect to the simulator on the engineer’s computer through a web interface. Additionally, we discovered that the OLP does not enforce access control for accessible computer resources, allowing remote attackers to exploit vulnerabilities like path traversal to gain unauthorized access to system resources, as shown in Figure 8.
 Figure 8. Resources of the Remote Unauthorized Access System
Figure 8. Resources of the Remote Unauthorized Access System
Security Recommendation
This vulnerability will impact FANUC ROBOGUIDE-HandlingPRO Versions 9 Rev.ZD and prior versions. TXOne Networks has notified FANUC through CISA, and due to the proactive handling by FANUC, the patch has been completed. It is recommended that customers update to the latest version [15]. At the same time, the TXOne Networks’ Edge series solution can also detect and block this attack, preventing devices from being exploited by the vulnerability, as shown in Figure 9.
 Figure 9. TXOne Networks’ Edge Series Solution Successfully Detects and Blocks This Vulnerability
Figure 9. TXOne Networks’ Edge Series Solution Successfully Detects and Blocks This Vulnerability
References
[1] TXOne Networks blog, “Potential Threats to Automated Factories”, TXOne Networks, Aug 24 2022, Accessed Apr 13 2023
[2] TXOne Networks blog, “Anatomy of Robots: Cybersecurity in the Modern Factory”, TXOne Networks, Mar 6 2023, Accessed Apr 13 2023
[3] Elizabeth Kurkowski, Alyxandra Van Stockum, Joel Dawson, Curtis Taylor, Tricia Schulz, Sujeet Shenoi, “MANIPULATION OF G-CODE TOOLPATH FILES IN 3D PRINTERS: ATTACKS AND MITIGATIONS”, Springer, Nov 30 2022, Accessed Apr 13 2023
[4] Marco Balduzzi, “Uncovering Security Weak Spots in Industry 4.0 CNC Machines”, Trend Micro, Oct 24 2022, Accessed Apr 13 2023
[5] DOUG LYNCH, “Several Vulnerabilities Found in Common Android IDEs Including Android Studio, IntelliJ IDEA, and Eclipse”, XDA, Dec 7 2017, Accessed Apr 13 2023
[6] Swati Khandelwal, “World’s First Google Glass Spyware app unveiled”, The Hacker News, Mar 20 2014, Accessed Apr 13 2023
[7] Ben Lovejoy, “Google Glass could have been hijacked by a simple QR code”, 9to5Google, Jul 17 2013, Accessed Apr 13 2023
[8] Sharon Brizinov, “The Evil PLC Attack: Weaponizing PLCs”, DEFCON, Jun 7 2022, Accessed Apr 13 2023
[9] Maedotan, “Section 52 Releases an Open Source Forensics Tool for Siemens PLCs”, Microsoft, Nov 7 2022, Accessed Apr 13 2023
[10] Kaspersky ICS CERT, “The secrets of Schneider Electric’s UMAS protocol”, Kaspersky, Sep 29 2022, Accessed Apr 13 2023
[11] Federico Maggi, Marcello Pogliani, Davide Quarta, Stefano Zanero, Marco Balduzz, “OTRazor: Static Code Analysis for Vulnerability Discovery in Industrial Automation Scripts”, Black Hat, Aug 5 2020, Accessed Apr 13 2023
[12] Trend Micro’s Forward-looking Threat Research (FTR) team, “Rogue Robots – Testing the Limits of an Industrial Robot’s Security”, Trend Micro, May 3 2017, Accessed Apr 13 2023
[13] ICS-CERT Advisories, “ICSA-23-101-01, FANUC ROBOGUIDE-HandlingPRO”, CISA, Apr 11 2023, Accessed Apr 13 2023
[14] Tesla twitter, “In the body shop”, Tesla, Feb 14 2023, Accessed Apr 13 2023
[15] FANUC, “ROBOGUIDE-HandlingPRO”, FANUC, Accessed Apr 13 2023





